Figure 2 from Investigating the Effects of varying the Key Size on the Performance of AES Algorithm for Encryption of Data over a Communication Channel | Semantic Scholar
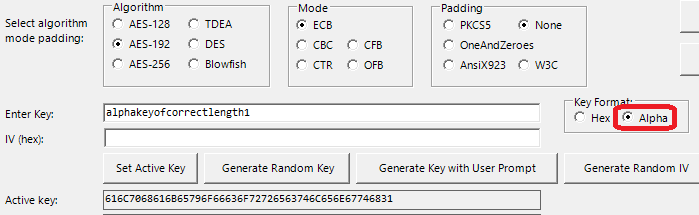
![PDF] Investigating the Effects of varying the Key Size on the Performance of AES Algorithm for Encryption of Data over a Communication Channel | Semantic Scholar PDF] Investigating the Effects of varying the Key Size on the Performance of AES Algorithm for Encryption of Data over a Communication Channel | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/da6c8b9a0aba014f56454994af710a708f61dc5e/3-Table2-1.png)
PDF] Investigating the Effects of varying the Key Size on the Performance of AES Algorithm for Encryption of Data over a Communication Channel | Semantic Scholar
![PDF] Investigating the Effects of varying the Key Size on the Performance of AES Algorithm for Encryption of Data over a Communication Channel | Semantic Scholar PDF] Investigating the Effects of varying the Key Size on the Performance of AES Algorithm for Encryption of Data over a Communication Channel | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/da6c8b9a0aba014f56454994af710a708f61dc5e/3-Table1-1.png)

![PDF] Key Lengths Contribution to The Handbook of Information Security | Semantic Scholar PDF] Key Lengths Contribution to The Handbook of Information Security | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/80d0c05336abbc51d095c1af2ae8143d493beacb/10-Table1-1.png)
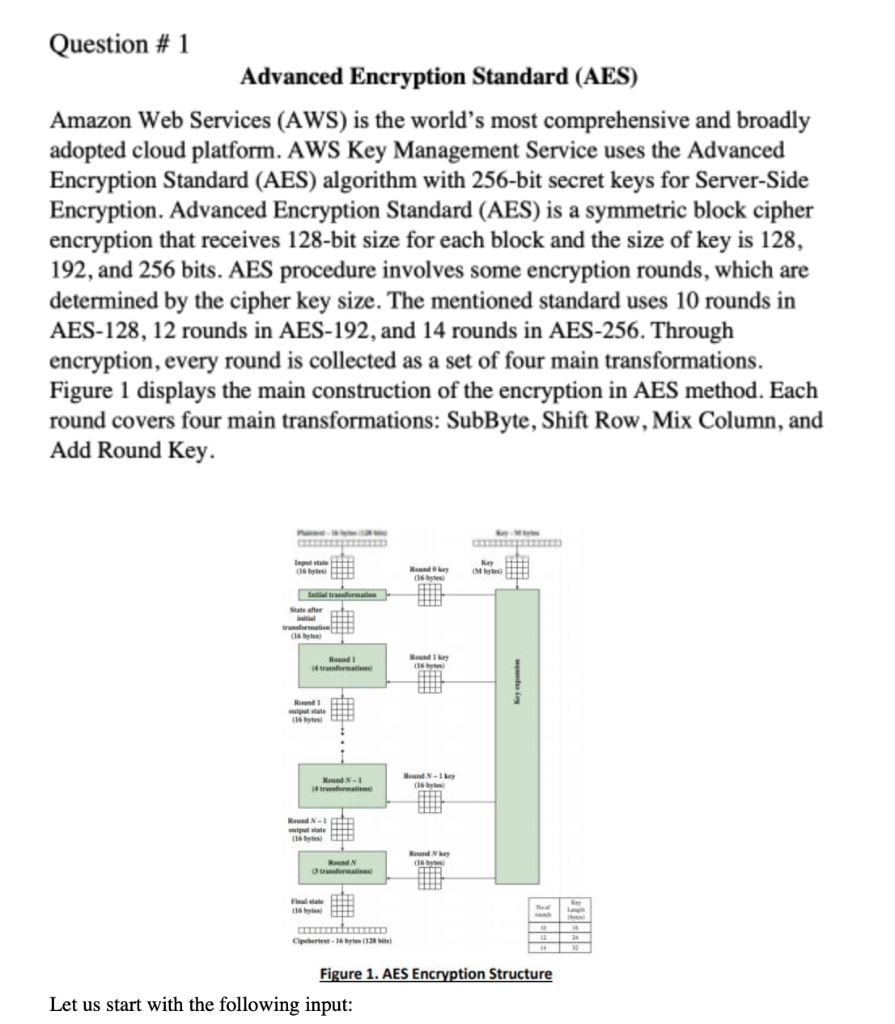






![AES speed at 128, 192 and 256-bit key sizes [12] | Download Scientific Diagram AES speed at 128, 192 and 256-bit key sizes [12] | Download Scientific Diagram](https://www.researchgate.net/publication/301324486/figure/fig3/AS:357937378807816@1462350330002/AES-speed-at-128-192-and-256-bit-key-sizes-12.png)